ISO 27001:2022 Failed Audit Recovery Plan
The email nobody wanted to receive
The email lands late on a Friday with a subject line that sounds harmless: “Transition Audit Outcome.”
The body is not harmless. The certification body has raised a major nonconformity. The ISO/IEC 27001 certificate is suspended or the transition decision cannot be closed. The auditor’s note is blunt: the Statement of Applicability does not justify excluded controls, the risk assessment does not reflect current context, and there is insufficient evidence that new regulatory obligations were considered.
Within an hour, the issue is no longer just a compliance problem. Sales is asking whether a public-sector tender is now at risk. Legal is reviewing customer contract clauses. The CISO is explaining why the SoA does not reconcile with the risk treatment plan. The CEO asks the only question that matters: “How fast can we fix this?”
For many organizations, the ISO 27001:2022 transition deadline passing did not create a theoretical gap. It created a live business continuity issue. A missed or failed ISO 27001:2022 transition audit can affect tender eligibility, supplier onboarding, cyber insurance, customer assurance, NIS2 readiness, DORA expectations, GDPR accountability, and board confidence.
The good news is that recovery is possible. The bad news is that document cosmetics will not work. Recovery must be treated as a disciplined ISMS corrective action program, not as a rushed policy rewrite.
At Clarysec, we organize this recovery around three connected assets:
- Zenith Blueprint: An Auditor’s 30-Step Roadmap, especially the Audit, Review & Improvement phase.
- Clarysec’s enterprise and SME policy library, which turns audit findings into governed obligations.
- Zenith Controls: The Cross-Compliance Guide, which helps connect ISO/IEC 27002:2022 control expectations with NIS2, DORA, GDPR, NIST-style assurance thinking, and COBIT 2019 governance perspectives.
This is the practical recovery plan for CISOs, compliance managers, auditors, founders, and business owners who missed the ISO 27001:2022 transition deadline or failed the transition audit.
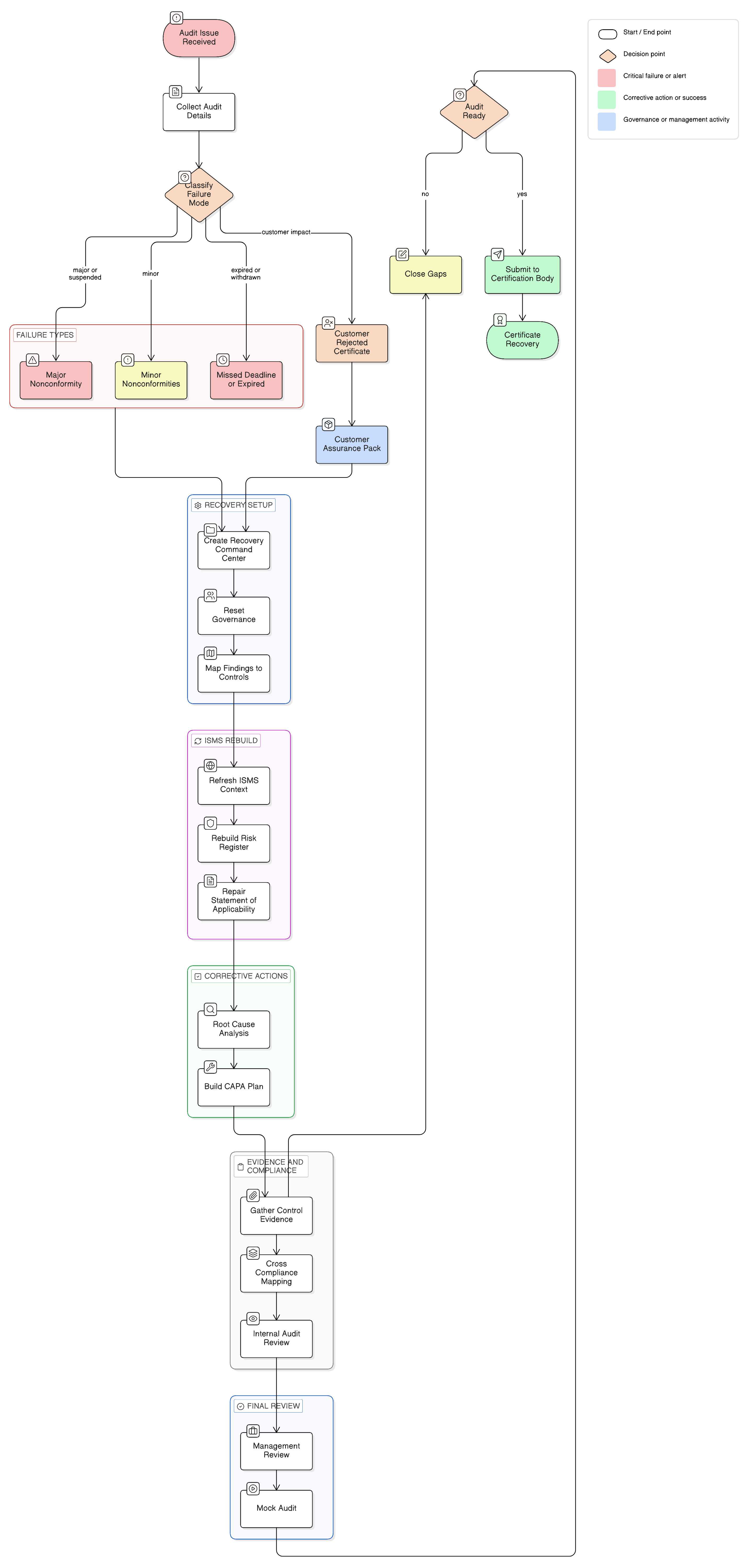
First, diagnose the failure mode
Before editing a single policy, classify the situation. Not every failed or missed transition has the same business impact or recovery path. Your first 24 hours should focus on obtaining the audit report, certification body decision, nonconformity wording, evidence requests, deadlines, and current certificate status.
| Situation | Business impact | Immediate action |
|---|---|---|
| Transition audit failed with major nonconformity | Certification decision may be blocked or certificate may be suspended until the issue is corrected | Open CAPA, perform root cause analysis, confirm evidence expectations with the certification body |
| Transition audit passed with minor nonconformities | Certification may continue if corrective actions are accepted | Close minor CAPAs quickly and update the ISMS evidence pack |
| Transition not completed before deadline | Certificate may no longer be valid or recognized | Confirm status with the certification body and plan transition or re-certification route |
| Surveillance audit revealed weak transition evidence | Certification may be at risk at the next decision point | Run a mock audit and update SoA, risk treatment, management review, and internal audit records |
| Customer rejected your certificate or transition evidence | Commercial risk, tender risk, and trust impact | Prepare a customer assurance pack with audit status, CAPA plan, target dates, and governance approval |
The recovery plan depends on the failure mode. A blocked certification decision requires targeted remediation. A suspended certificate requires urgent governance and evidence repair. A withdrawn or expired certificate may require a broader re-certification route.
In every case, map each issue to the relevant ISMS clause, Annex A control, risk record, policy owner, legal or contractual obligation, and evidence source.
This is where ISO/IEC 27001:2022 matters as a management system, not merely a control catalogue. Clauses 4 through 10 require the ISMS to understand context, interested parties, scope, leadership, risk planning, support, operation, performance evaluation, and continual improvement. If the transition failed, one of those management system links is usually broken.
Why ISO 27001:2022 transition audits fail
Failed transition audits usually cluster around repeat patterns. Many are not deeply technical. They are governance, traceability, ownership, and evidence failures.
| Finding pattern | What the auditor sees | What it usually means |
|---|---|---|
| Statement of Applicability not updated or not justified | Controls are marked applicable without rationale, or excluded without evidence | Control selection is not traceable to risk, regulation, or business need |
| Risk assessment did not reflect current obligations | NIS2, DORA, GDPR, customer contracts, cloud dependencies, or supplier risk are missing | Context and risk criteria were not refreshed |
| Management review is superficial | Minutes exist, but no decisions, resources, objectives, audit results, or risk changes are discussed | Leadership accountability is not operating |
| Internal audit did not test transition scope | Audit checklist is generic and does not cover updated controls, suppliers, cloud, resilience, or legal obligations | Performance evaluation is not sufficient |
| Supplier and cloud controls are weak | No due diligence, contract review, exit planning, or ongoing monitoring | Operational control over externally provided services is incomplete |
| Incident response is not aligned with regulatory reporting | No 24-hour or 72-hour escalation logic, no DORA or GDPR decision tree, no evidence of exercises | Incident management is not connected to legal reporting |
| CAPA process is weak | Findings are closed by document edits only | Root cause was not eliminated |
The failed audit is a signal that the ISMS did not adapt quickly enough to the organization’s real operating environment.
ISO/IEC 27005:2022 is useful in recovery because it reinforces the importance of establishing context using legal, regulatory, sector-specific, contractual, internal, and existing control requirements. It also supports risk criteria that account for legal duties, suppliers, privacy, human factors, business objectives, and management-approved risk appetite.
In practical terms, transition recovery begins with refreshed context and risk criteria, not with a new version number on an old document.
Step 1: Freeze the audit record and create a recovery command center
The first operational mistake after a failed audit is evidence chaos. Teams start searching inboxes, shared drives, ticketing systems, chat messages, personal folders, and old audit packs. Auditors interpret this as a sign that the ISMS is not controlled.
Clarysec’s SME Audit and Compliance Monitoring Policy - SME is explicit about evidence control:
“All evidence must be stored in a centralized audit folder.”
From section “Policy Implementation Requirements”, policy clause 6.2.1.
That centralized audit folder becomes the recovery cockpit. It should include:
- Certification body report and correspondence.
- Certificate status confirmation.
- Nonconformity register.
- CAPA log.
- Updated risk assessment.
- Updated risk treatment plan.
- Updated Statement of Applicability.
- Internal audit report.
- Management review minutes.
- Policy approval records.
- Evidence for each applicable Annex A control.
- Customer assurance pack, if commercial commitments are affected.
For enterprise environments, Clarysec’s Audit and Compliance Monitoring Policy sets the same governance expectation:
“All findings shall result in a documented CAPA that includes:”
From section “Policy Implementation Requirements”, policy clause 6.2.1.
The wording introduces a structured corrective action expectation. The essential point is simple: every audit finding must become a governed CAPA item, not an informal task in someone’s notebook.
For SMEs, leadership involvement is equally important:
“The GM must approve a corrective action plan and track its implementation.”
From Audit and Compliance Monitoring Policy - SME, section “Governance Requirements”, policy clause 5.4.2.
This matters because ISO 27001:2022 does not treat leadership as symbolic. Top management must establish policy, align objectives with business strategy, provide resources, communicate the importance of information security, assign responsibilities, and promote continual improvement.
If the failed transition is treated as “the compliance person’s issue,” the next audit will expose weak leadership accountability again.
Step 2: Rebuild context, obligations, and risk
A failed transition audit often means the ISMS context no longer reflects the organization’s world. The business may have moved to cloud platforms, added new suppliers, entered regulated markets, processed more personal data, or become relevant to customers under NIS2 or DORA. If those changes are missing from the ISMS, the risk assessment and SoA will be incomplete.
Clarysec’s Legal and Regulatory Compliance Policy sets the baseline:
“All legal and regulatory obligations must be mapped to specific policies, controls, and owners within the Information Security Management System (ISMS).”
From section “Policy Implementation Requirements”, policy clause 6.2.1.
This clause is critical after a transition failure. ISO 27001:2022 clauses 4.1 to 4.3 require organizations to consider internal and external issues, interested parties, requirements, interfaces, dependencies, and scope. Legal, regulatory, and contractual obligations are not side notes. They shape the ISMS.
NIS2 Article 21 requires appropriate and proportionate technical, operational, and organizational measures, including risk analysis, policies, incident handling, backup, disaster recovery, crisis management, supply-chain security, secure development, vulnerability handling, effectiveness assessments, cyber hygiene, training, cryptography, HR security, access control, asset management, and secure communications. Article 20 places responsibility at management-body level. Article 23 creates staged significant-incident reporting, including early warning, incident notification, updates, and final reporting.
DORA applies directly to financial entities from 17 January 2025 and covers ICT risk management, major incident reporting, resilience testing, ICT third-party risk, contractual requirements, and oversight of critical ICT third-party providers. For financial entities in scope, DORA becomes a core driver of ICT governance, supplier control, testing, incident classification, and management accountability.
GDPR adds accountability for personal data. Article 5 requires lawful, fair, transparent, limited, accurate, retention-aware, and secure processing, with demonstrable compliance. Article 4 defines personal data breach in a way that directly affects incident classification. Article 6 requires lawful basis mapping, and Article 9 adds heightened requirements for special category data.
This does not mean creating separate compliance universes. It means using ISO 27001:2022 as the integrated management system and mapping obligations into one risk and control architecture.
Clarysec’s Risk Management Policy connects risk treatment directly to control selection:
“Control decisions resulting from the risk treatment process shall be reflected in the SoA.”
From section “Policy Implementation Requirements”, policy clause 6.5.1.
A failed audit is also a reason to review the risk management process itself. Clarysec’s SME Risk Management Policy - SME identifies this trigger:
“A major incident or audit finding reveals gaps in risk management”
From section “Review and Update Requirements”, policy clause 9.2.1.1.
In recovery mode, that means the risk register, risk criteria, treatment plan, and SoA must be rebuilt together.
Step 3: Repair the SoA as the traceability spine
In most failed transitions, the Statement of Applicability is the first document to inspect. It is also one of the first documents auditors sample. A weak SoA tells the auditor that control selection is not risk-based.
The Zenith Blueprint gives a practical instruction in the Audit, Review & Improvement phase, Step 24, Audit, Review & Improvement:
“Your SoA should be consistent with your Risk Register and Risk Treatment Plan. Double-check that every control you chose as a risk treatment is marked ‘Applicable’ in the SoA. Conversely, if a control is marked ‘Applicable’ in the SoA, you should have a rationale for it - usually a mapped risk, a legal/regulatory requirement, or a business need.”
From Zenith Blueprint: An Auditor’s 30-Step Roadmap, Audit, Review & Improvement phase, Step 24.
That is the recovery principle. The SoA is not a formality. It is the traceability spine between risks, obligations, controls, implementation evidence, and audit conclusions.
A practical SoA repair exercise should follow this sequence:
- Export the current SoA.
- Add columns for risk ID, regulatory obligation, business requirement, policy reference, evidence location, owner, implementation status, and last tested date.
- For every applicable control, map at least one defensible rationale.
- For every excluded control, write a specific exclusion reason.
- Reconcile the SoA with the risk treatment plan.
- Reconcile the SoA with internal audit results.
- Ask the hard question: if an auditor samples this row, can we prove it in five minutes?
A defensible SoA row should look like this:
| SoA field | Example recovery entry |
|---|---|
| Control rationale | Applicable due to cloud hosting, payment processor, outsourced support, and contractual customer security commitments |
| Risk link | R-014 third-party service disruption, R-021 supplier data exposure, R-027 regulatory breach due to processor failure |
| Obligation link | NIS2 supply-chain security, DORA ICT third-party risk where applicable, GDPR processor accountability |
| Policy link | Third-party and supplier security policy, contract review procedure, vendor assessment checklist |
| Evidence | Supplier register, risk ratings, due diligence questionnaire, signed DPA, SOC report review, exit plan, annual review record |
| Owner | Vendor Manager, CISO, Legal |
| Testing | Internal audit sample of top five critical suppliers completed, exceptions logged in CAPA |
| Status | Implemented with two corrective actions open for contract updates |
This row tells a recovery story. It shows business context, risk logic, regulatory relevance, ownership, implementation, testing, and remaining action.
For exclusions, the same discipline applies. For example, if the organization performs no in-house software development, an exclusion for ISO/IEC 27002:2022 control 8.25 Secure development life cycle and control 8.28 Secure coding may be defensible, but only if it is true, documented, and supported by evidence that software is commercial off-the-shelf or fully outsourced with supplier controls in place.
Step 4: Perform root cause analysis, not document cosmetics
A failed transition audit is rarely caused by one missing file. It is usually caused by a broken process.
The Zenith Blueprint, Audit, Review & Improvement phase, Step 27, Audit Findings - Analysis & Root Cause, states:
“For each nonconformity (major or minor) identified, think about why it happened - this is critical for effective correction.”
From Zenith Blueprint, Audit, Review & Improvement phase, Step 27.
If the finding says “SoA justifications are missing,” the correction may be to update the SoA. But the root cause may be that asset owners were not involved in risk assessment, legal obligations were not mapped, or the compliance team maintained the SoA in isolation.
A useful recovery table separates weak corrections from true corrective action:
| Audit finding | Bad correction | Proper root cause question | Better corrective action |
|---|---|---|---|
| SoA not aligned with risk treatment | Update SoA wording | Why was SoA not reconciled with risk treatment? | Add quarterly SoA-risk reconciliation owned by ISMS Manager |
| No supplier evaluations | Upload one questionnaire | Why were suppliers not reviewed? | Assign supplier owner, define risk tiering, complete reviews, monitor annually |
| Management review incomplete | Add agenda item retroactively | Why did management review not cover transition status? | Update management review template and schedule quarterly governance review |
| Incident reporting not tested | Edit incident procedure | Why was reporting not exercised? | Run tabletop with NIS2, DORA, and GDPR decision points and keep evidence |
| Internal audit too narrow | Expand checklist | Why did audit planning miss transition scope? | Approve a risk-based audit plan covering regulation, suppliers, cloud, and resilience |
This is where credibility returns. Auditors do not expect perfection. They expect a controlled system that detects, corrects, learns, and improves.
Step 5: Build CAPA an auditor can trust
Corrective and preventive action is where many organizations regain control. The CAPA register should become the recovery roadmap and the primary evidence that the failed audit was handled systematically.
The Zenith Blueprint, Audit, Review & Improvement phase, Step 29, Continual Improvement, explains the structure:
“Make sure each corrective action is specific, assignable, and time-bound. Essentially, you are creating a mini project for each issue.”
From Zenith Blueprint, Audit, Review & Improvement phase, Step 29.
Your CAPA log should include:
- Finding ID.
- Source audit.
- Clause or control reference.
- Severity.
- Issue description.
- Immediate correction.
- Root cause.
- Corrective action.
- Preventive action, where relevant.
- Owner.
- Due date.
- Evidence required.
- Status.
- Effectiveness check.
- Management approval.
Clarysec’s Audit and Compliance Monitoring Policy - SME also identifies a major nonconformity as a review trigger:
“A certification audit or surveillance audit results in a major nonconformity”
From section “Review and Update Requirements”, policy clause 9.2.2.
If the transition audit produced a major nonconformity, review the audit and compliance monitoring process itself. Why did internal audit not detect the issue first? Why did management review not escalate it? Why did the SoA not reveal the evidence gap?
That is how a failed audit becomes a stronger ISMS.
Step 6: Use Zenith Controls to connect ISO evidence to cross-compliance
A re-audit does not happen in isolation. Customers, regulators, insurers, and internal governance teams may all look at the same evidence from different angles. This is where Zenith Controls is valuable as a cross-compliance guide. It helps teams stop treating ISO 27001, NIS2, DORA, GDPR, NIST-style assurance, and COBIT 2019 governance as separate checklists.
Three ISO/IEC 27002:2022 controls are especially relevant in transition recovery.
| ISO/IEC 27002:2022 control | Recovery relevance | Evidence to prepare |
|---|---|---|
| 5.31 Legal, statutory, regulatory and contractual requirements | Confirms obligations are identified, documented, and linked into the ISMS | Legal register, contract obligations, regulatory map, policy-owner matrix, SoA rationale |
| 5.35 Independent review of information security | Confirms review activity is objective, scoped, competent, and acted upon | Internal audit plan, independent review report, auditor competence, CAPA records, management reporting |
| 5.36 Compliance with policies, rules and standards for information security | Confirms policies are not just published, but monitored and enforced | Policy attestation, exception logs, monitoring reports, disciplinary workflow, compliance testing |
In Zenith Controls, ISO/IEC 27002:2022 control 5.31 is tied directly to privacy and PII:
“5.34 covers compliance with data protection laws (e.g. GDPR), which is one category of legal requirements under 5.31.”
From Zenith Controls, control 5.31, ties to other controls.
For recovery, this means the legal register must not sit outside the ISMS. It must drive the SoA, risk treatment plan, policy set, control ownership, and audit evidence.
For ISO/IEC 27002:2022 control 5.35, Zenith Controls highlights that independent review often reaches into operational evidence:
“Independent reviews under 5.35 frequently assess the adequacy of logging and monitoring activities.”
From Zenith Controls, control 5.35, ties to other controls.
That is practical. An auditor may start with governance and then sample logs, alerts, monitoring records, access reviews, incident tickets, backup tests, supplier reviews, and management decisions.
For ISO/IEC 27002:2022 control 5.36, Zenith Controls explains the relationship with internal policy governance:
“Control 5.36 serves as the enforcement mechanism for the rules defined under 5.1.”
From Zenith Controls, control 5.36, ties to other controls.
This is where many transition programs fail. Policies exist, but compliance with them is not monitored. Procedures exist, but exceptions are not captured. Controls are declared, but not tested.
Step 7: Prepare for different audit lenses
A strong recovery pack should survive more than one auditor’s perspective. ISO certification auditors, DORA supervisors, NIS2 reviewers, GDPR stakeholders, customer assurance teams, NIST-oriented assessors, and COBIT 2019 governance reviewers may all ask different questions about the same evidence.
| Auditor lens | Likely question | Evidence that helps |
|---|---|---|
| ISO 27001:2022 auditor | Is the ISMS effective, risk-based, scoped correctly, reviewed by leadership, and continually improved? | Scope, context, interested parties, risk assessment, SoA, treatment plan, internal audit, management review, CAPA |
| NIST-oriented assessor | Are governance, risk identification, protection, detection, response, and recovery activities operating coherently? | Asset inventory, risk register, access controls, logging, monitoring, incident playbooks, recovery tests |
| COBIT 2019 or ISACA-style auditor | Are governance objectives, ownership, performance monitoring, risk management, and compliance assurance embedded? | RACI, approved objectives, metrics, audit plan, management reporting, control ownership, issue tracking |
| NIS2 compliance reviewer | Has management approved and overseen proportionate cybersecurity risk measures and incident reporting workflows? | Board minutes, risk measures, supplier controls, incident escalation, training, continuity and crisis evidence |
| DORA reviewer | Is ICT risk management documented, tested, supplier-aware, and integrated into governance? | ICT risk framework, resilience tests, incident classification, ICT contract register, exit plans, audit rights |
| GDPR reviewer | Can the organization demonstrate accountability for personal data protection and breach response? | RoPA, lawful basis mapping, DPIAs where needed, processor contracts, breach logs, technical and organizational measures |
The goal is not duplicate evidence. A single SoA row for logging and monitoring can support ISO evidence, NIST-style detection expectations, DORA incident handling, NIS2 effectiveness assessment, and GDPR breach detection. A single supplier risk file can support ISO supplier controls, DORA ICT third-party risk, NIS2 supply-chain security, and GDPR processor accountability.
This is the practical value of cross-compliance.
Step 8: Run a final documentation review and mock audit
Before returning to the certification body, run a hard internal challenge. The Zenith Blueprint, Audit, Review & Improvement phase, Step 30, Certification Preparation - Final Review & Mock Audit, recommends checking ISO 27001:2022 clauses 4 through 10 one by one and validating evidence for every applicable Annex A control.
It advises:
“Check Annex A controls: ensure that for each control you marked ‘Applicable’ in the SoA, you have something to show for it.”
From Zenith Blueprint, Audit, Review & Improvement phase, Step 30.
The final review should be direct:
- Can every applicable control be explained?
- Can every excluded control be justified?
- Can residual risk acceptance be shown?
- Did management review the transition failure, resources, objectives, audit results, and corrective actions?
- Did internal audit test the updated SoA and risk treatment plan?
- Are supplier, cloud, continuity, incident, privacy, access, vulnerability, logging, and monitoring controls evidenced?
- Are policies approved, current, communicated, and version controlled?
- Are CAPAs linked to root causes and effectiveness checks?
- Can evidence be found quickly in the centralized audit folder?
Clarysec’s Information Security Policy provides the governance baseline:
“The organization shall implement and maintain an Information Security Management System (ISMS) in accordance with ISO/IEC 27001:2022 Clauses 4 through 10.”
From section “Policy Implementation Requirements”, policy clause 6.1.1.
For SMEs, review must also track certification requirements and regulatory change. Clarysec’s Information Security Policy - SME states:
“This policy must be reviewed by the General Manager (GM) at least annually to ensure continued compliance with ISO/IEC 27001 certification requirements, regulatory changes (such as GDPR, NIS2, and DORA), and evolving business needs.”
From section “Review and Update Requirements”, policy clause 9.1.1.
That is exactly what many transition programs missed: ISO, regulation, and business change move together.
What to tell customers while you recover
If a failed or missed transition affects customer contracts, silence is dangerous. You do not need to disclose every internal audit detail, but you should provide controlled assurance.
A customer communication pack should include:
- Current certification status confirmed by the certification body.
- Transition audit status and high-level remediation plan.
- Confirmation that a CAPA process is active and management-approved.
- Target dates for corrective actions and audit closure.
- Statement that the ISMS remains operational.
- Security assurance contact point.
- Updated security policy statement, if appropriate.
- Evidence of compensating controls for any high-risk area.
Avoid vague claims such as “we are fully compliant” while the audit is unresolved. Say what is true: the ISMS is operating, corrective action is approved, evidence is being consolidated, and a closure review or re-audit is scheduled.
This is especially important if customers rely on you as a supplier in NIS2-relevant sectors such as digital infrastructure, cloud, data centres, content delivery networks, DNS, trust services, public electronic communications, managed services, or managed security services. If your audit status affects their supply-chain risk, they need credible assurance.
A 10-day practical recovery sprint
Timelines vary by certification body, severity, scope, and evidence maturity. But the recovery sequence is reliable.
| Day | Activity | Output |
|---|---|---|
| 1 | Collect audit report, confirm certificate status, open centralized audit folder | Recovery command center |
| 2 | Classify findings, assign owners, brief management | Approved recovery governance |
| 3 | Refresh context, obligations, interested parties, and scope assumptions | Updated context and compliance map |
| 4 | Reconcile risk assessment and risk treatment plan | Updated risk register and treatment plan |
| 5 | Repair SoA with rationale, exclusions, evidence, and owners | Audit-ready SoA |
| 6 | Execute root cause analysis for all findings | Root cause log |
| 7 | Build CAPA plan with target dates and evidence requirements | CAPA register |
| 8 | Gather and test evidence for priority controls | Evidence pack |
| 9 | Conduct management review and approve residual risks | Management review minutes |
| 10 | Run mock audit and prepare certification body response | Re-audit readiness pack |
Do not submit the response until it tells a coherent story. The auditor should be able to follow the chain from finding to root cause, from root cause to corrective action, from corrective action to evidence, and from evidence to management review.
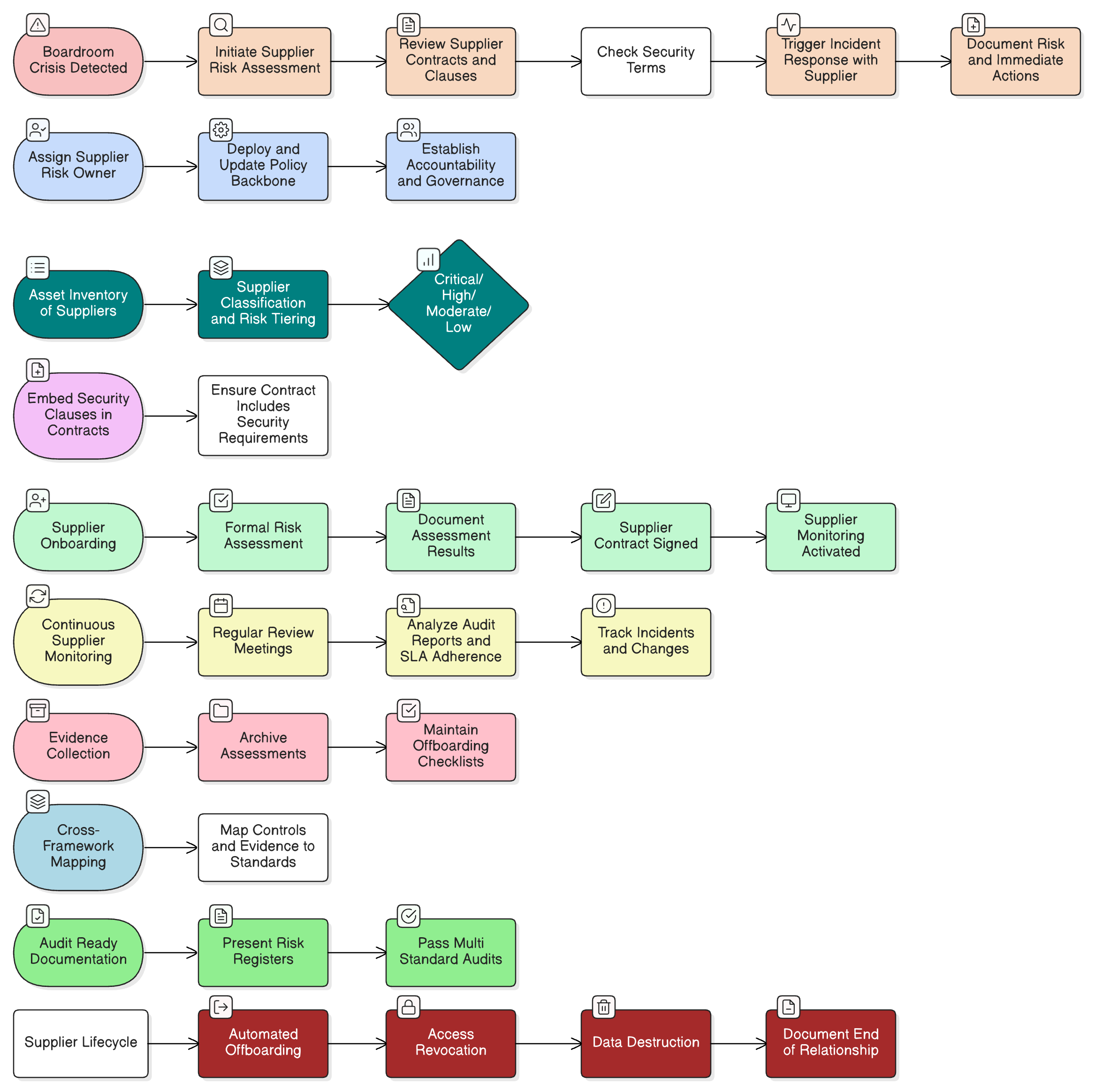
The Clarysec recovery workflow
When Clarysec supports a missed or failed ISO 27001:2022 transition, we organize the work into a focused recovery workflow.
| Recovery phase | Clarysec asset | Output |
|---|---|---|
| Audit triage | Zenith Blueprint Steps 24, 27, 29, 30 | Finding classification, evidence map, audit closure plan |
| Governance reset | Information Security Policy, Audit and Compliance Monitoring Policy | Approved responsibilities, management involvement, centralized evidence folder |
| Risk refresh | Risk Management Policy, ISO/IEC 27005:2022 method | Updated context, criteria, risk register, treatment plan |
| SoA repair | Zenith Blueprint Step 24, Risk Management Policy | Traceable SoA with risk, obligation, owner, evidence, status |
| Cross-compliance mapping | Zenith Controls | NIS2, DORA, GDPR, NIST-style, and COBIT 2019 assurance alignment |
| CAPA execution | Zenith Blueprint Step 29, Audit policies | Root cause, corrective action, owner, deadline, effectiveness check |
| Mock audit | Zenith Blueprint Step 30 | Re-audit readiness pack and customer assurance pack |
This is not about manufacturing paperwork. It is about restoring confidence that the ISMS is governed, risk-based, evidenced, and improving.
Final advice: treat the failed transition as a stress test
A missed ISO 27001:2022 transition deadline or failed transition audit feels like a crisis, but it is also a diagnostic opportunity. It shows whether your ISMS can absorb change, integrate legal obligations, manage suppliers, prove control operation, and learn from failure.
The organizations that recover fastest do three things well:
- They centralize evidence and stop the chaos.
- They rebuild traceability between risk, SoA, controls, policies, and obligations.
- They handle audit findings through disciplined CAPA and management review.
The organizations that struggle try to solve the problem by editing documents without fixing ownership, monitoring, evidence, or root cause.
If you missed the deadline or failed your transition audit, your next step is not panic. It is structured recovery.
Clarysec can help you run transition audit triage, rebuild your SoA, map NIS2, DORA, GDPR, NIST-style, and COBIT 2019 expectations through Zenith Controls, execute corrective actions with Zenith Blueprint, and align policy evidence using Information Security Policy, Audit and Compliance Monitoring Policy, Risk Management Policy, and Legal and Regulatory Compliance Policy.
Your certificate issue can be repaired. Your ISMS can become stronger than it was before the audit. If your transition audit is unresolved, start the recovery assessment now, consolidate your evidence, and prepare a re-audit pack that proves your ISMS is not just documented, but working.
Frequently Asked Questions
About the Author

Igor Petreski
Compliance Systems Architect, Clarysec LLC
Igor Petreski is a cybersecurity leader with over 30 years of experience in information technology and a dedicated decade specializing in global Governance, Risk, and Compliance (GRC).Core Credentials & Qualifications:• MSc in Cyber Security from Royal Holloway, University of London• PECB-Certified ISO/IEC 27001 Lead Auditor & Trainer• Certified Information Systems Auditor (CISA) from ISACA• Certified Information Security Manager (CISM) from ISACA • Certified Ethical Hacker from EC-Council