#Audit
Articles tagged with "Audit"
27 articles
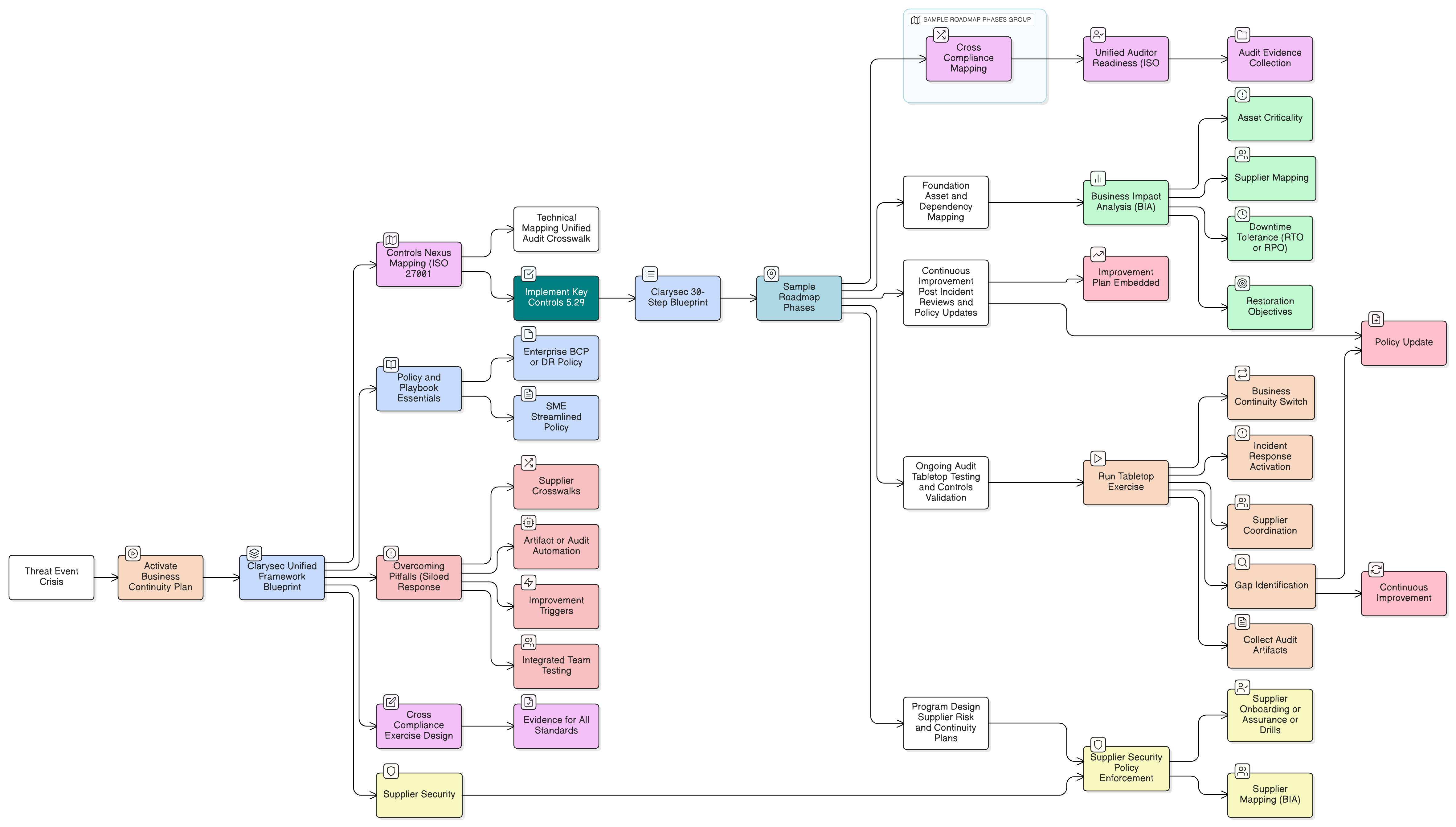
CISOs and compliance leaders face new urgency from DORA and NIS2. This flagship Clarysec guide demonstrates how to build robust operational resilience, across plans, controls, supplier management, and audits, by unifying global standards with tested action steps.
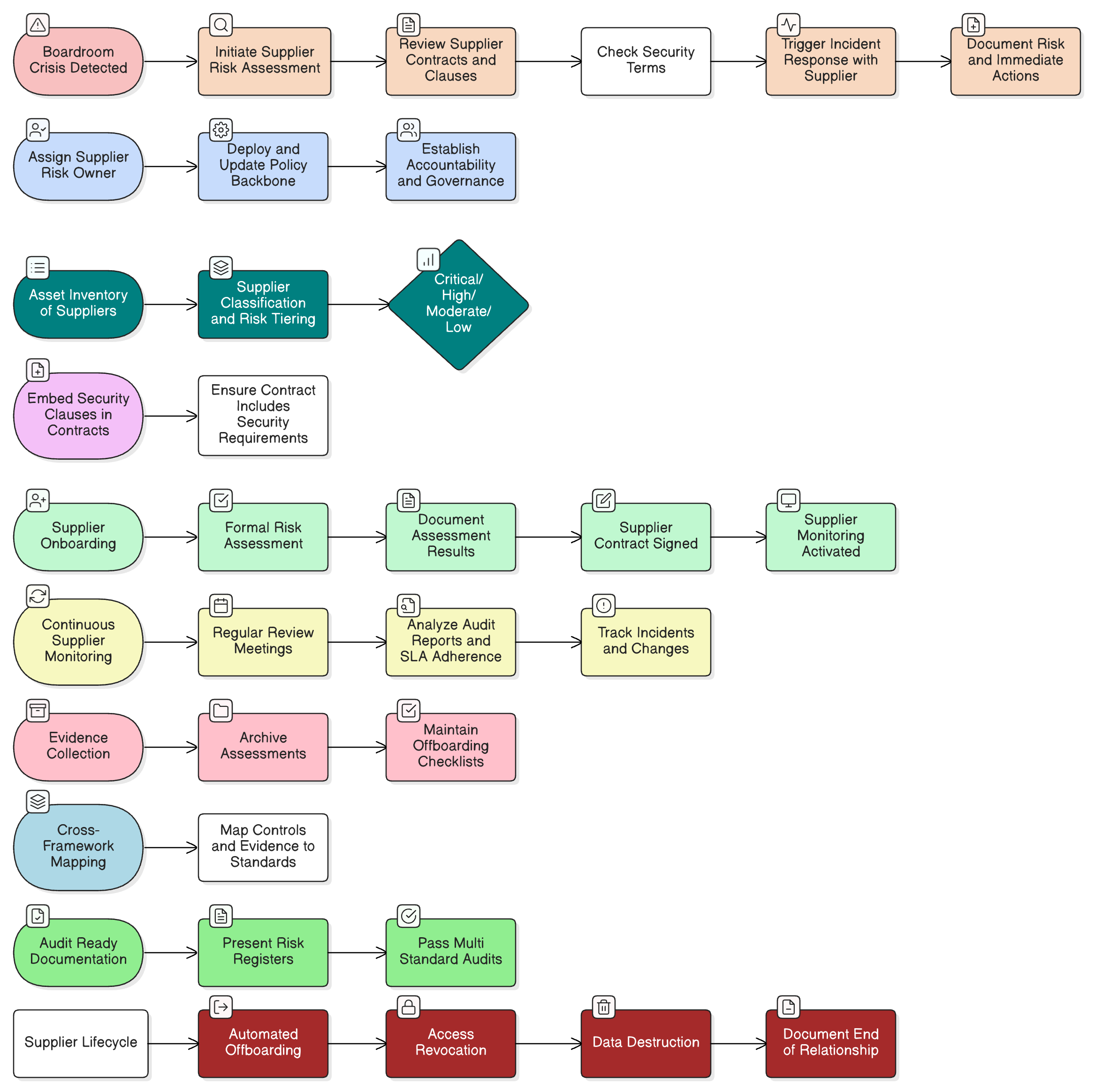
A comprehensive guide to operationalizing supplier risk management, from boardroom crises to cross-framework audit triumphs, using real-world scenarios, Clarysec’s Zenith toolkits, and actionable blueprints that secure the supply chain throughout its entire lifecycle.
Master ISO 27001 incident response with our CISO’s guide. Learn from a real-world manufacturing scenario, from preparation to post-breach analysis and compliance.
A guide for manufacturers on building a robust, ISO 27001-aligned incident response plan to protect operations and ensure compliance.
Uncover the truth behind the top 7 GDPR myths of 2025. Our expert guide debunks common misconceptions about consent, data breaches, and compliance.
Network security is essential for ISO 27001 and NIS2 compliance, underpinning risk management, resilience, and regulatory assurance for modern organisations.
How SMEs can implement access control and MFA in line with ISO 27001:2022 A.8.2, A.8.3 and GDPR Article 32, reducing risk and ensuring regulatory compliance.
Learn how SMEs can leverage the ISO/IEC 27001:2022 framework to build a robust ISMS that systematically addresses GDPR requirements for data protection.
Introduction
ISO 27001 is the international standard for information security management systems (ISMS). This comprehensive guide will walk you through the essential steps to implement ISO 27001 in your organization, from initial planning to certification.
What is ISO 27001?
ISO 27001 provides a systematic approach to managing sensitive company information and ensuring it remains secure. It includes people, processes, and IT systems by applying a risk management process.
Key Benefits
- Enhanced Security: Systematic approach to protecting information assets
- Regulatory Compliance: Meets various regulatory requirements
- Business Continuity: Reduces the risk of security incidents
- Competitive Advantage: Demonstrates commitment to information security
- Customer Trust: Builds confidence with clients and partners
Implementation Process
1. Gap Analysis
Start by conducting a thorough gap analysis to understand your current security posture: