#ISMS
Articles tagged with "ISMS"
29 articles
This flagship article walks CISOs and compliance leaders through a real-world approach to building a NIS2-compliant supply chain risk program. It combines regulatory insights, actionable controls, and Clarysec’s expert guidance to turn your supply chain from a critical vulnerability into a resilient, auditable asset.
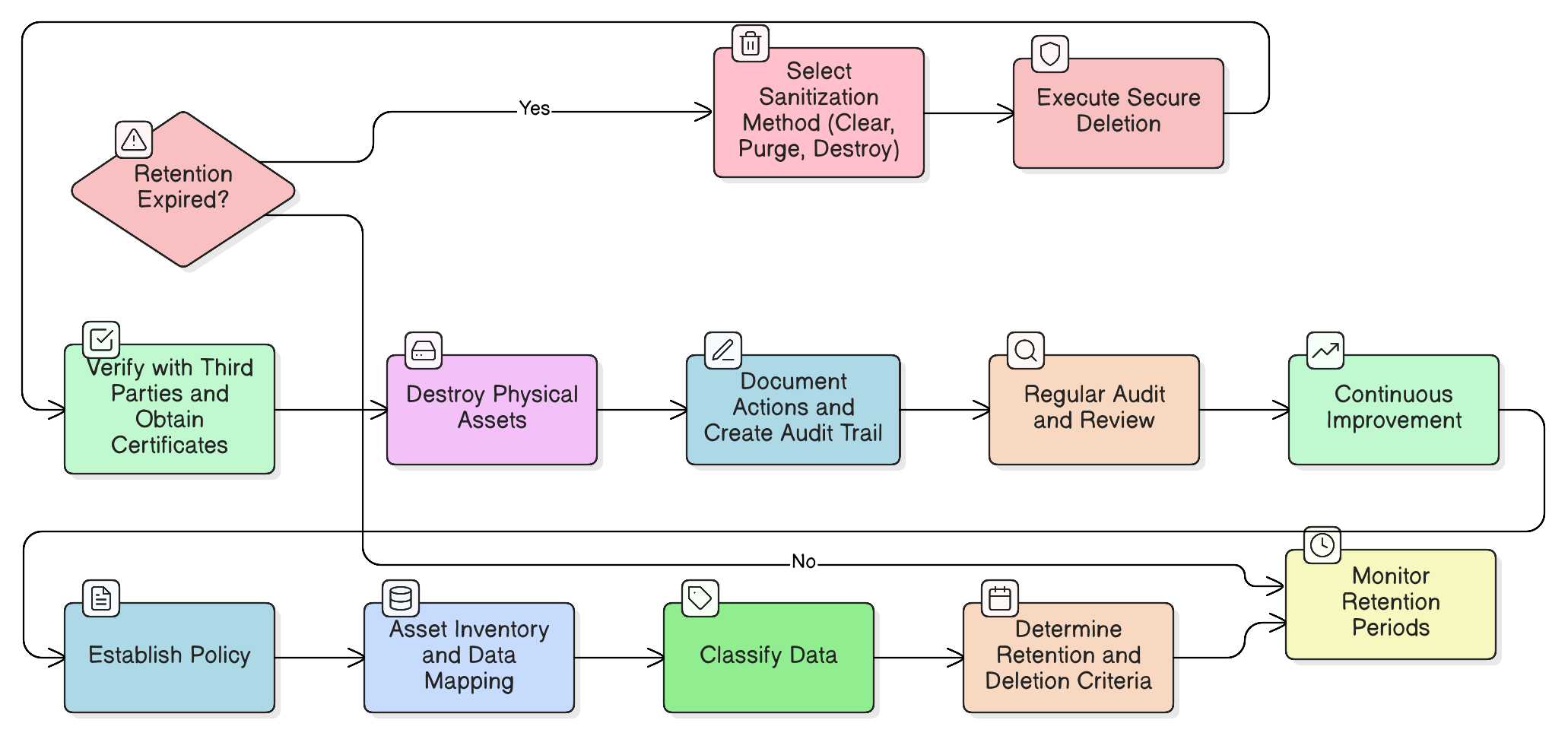
Transform your legacy data risk into a strategic advantage. This in-depth guide covers everything from policy creation and media sanitization to building an audit-proof trail for data disposal, combining Clarysec’s expert roadmaps and policy toolkits.
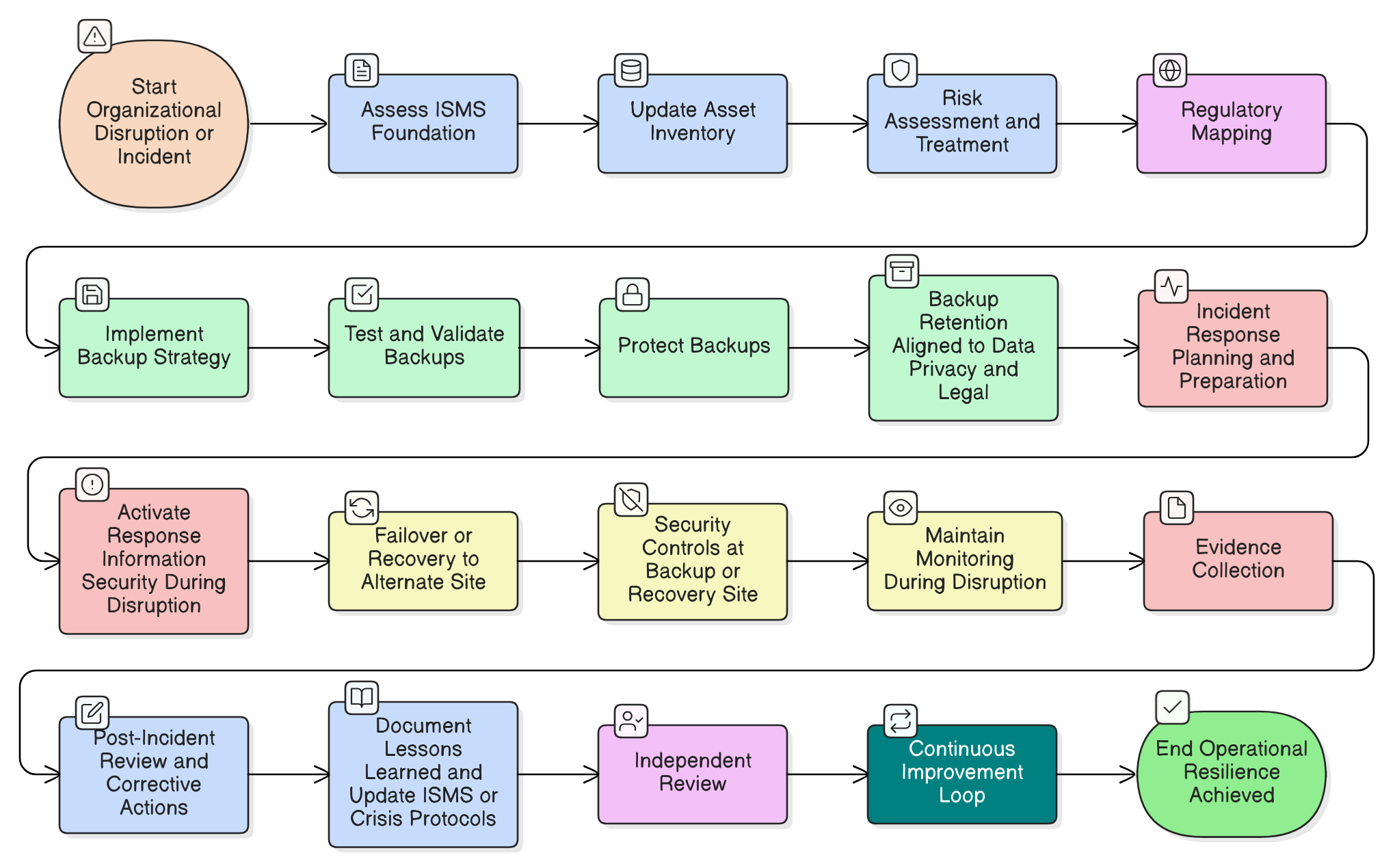
A ransomware attack hits during a board meeting. Your backups are working, but is your security? Discover how to implement ISO/IEC 27001:2022’s resilience controls to maintain security under pressure, satisfy auditors, and meet stringent DORA and NIS2 requirements with Clarysec’s expert roadmap.
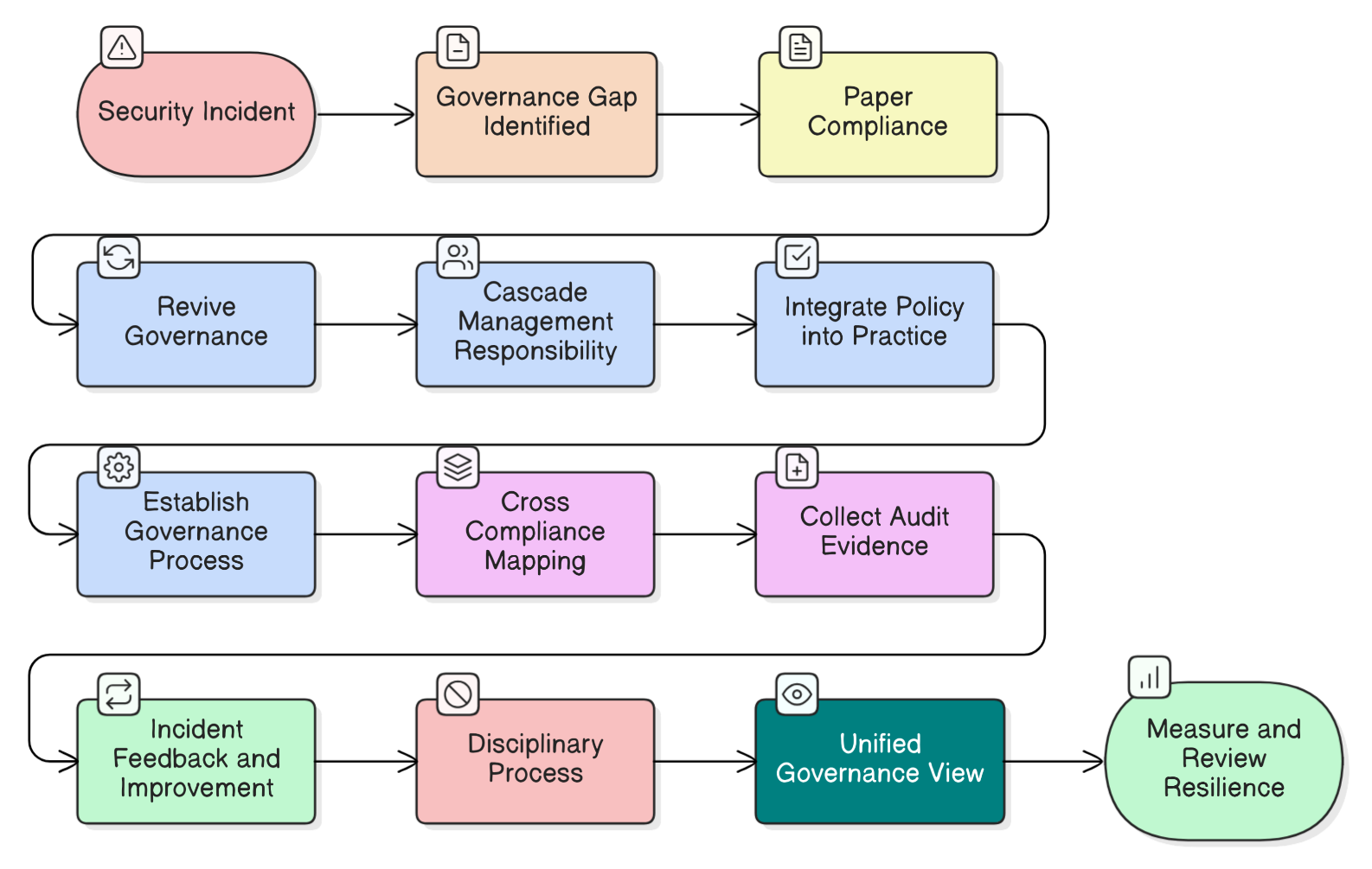
Compliance checklists don’t prevent breaches, active governance does. We break down the CISO’s biggest governance myths using a real-world incident, providing a roadmap to build true enterprise resilience with actionable steps, policy examples, and cross-compliance mappings for ISO 27001:2022, NIS2, DORA, and more.
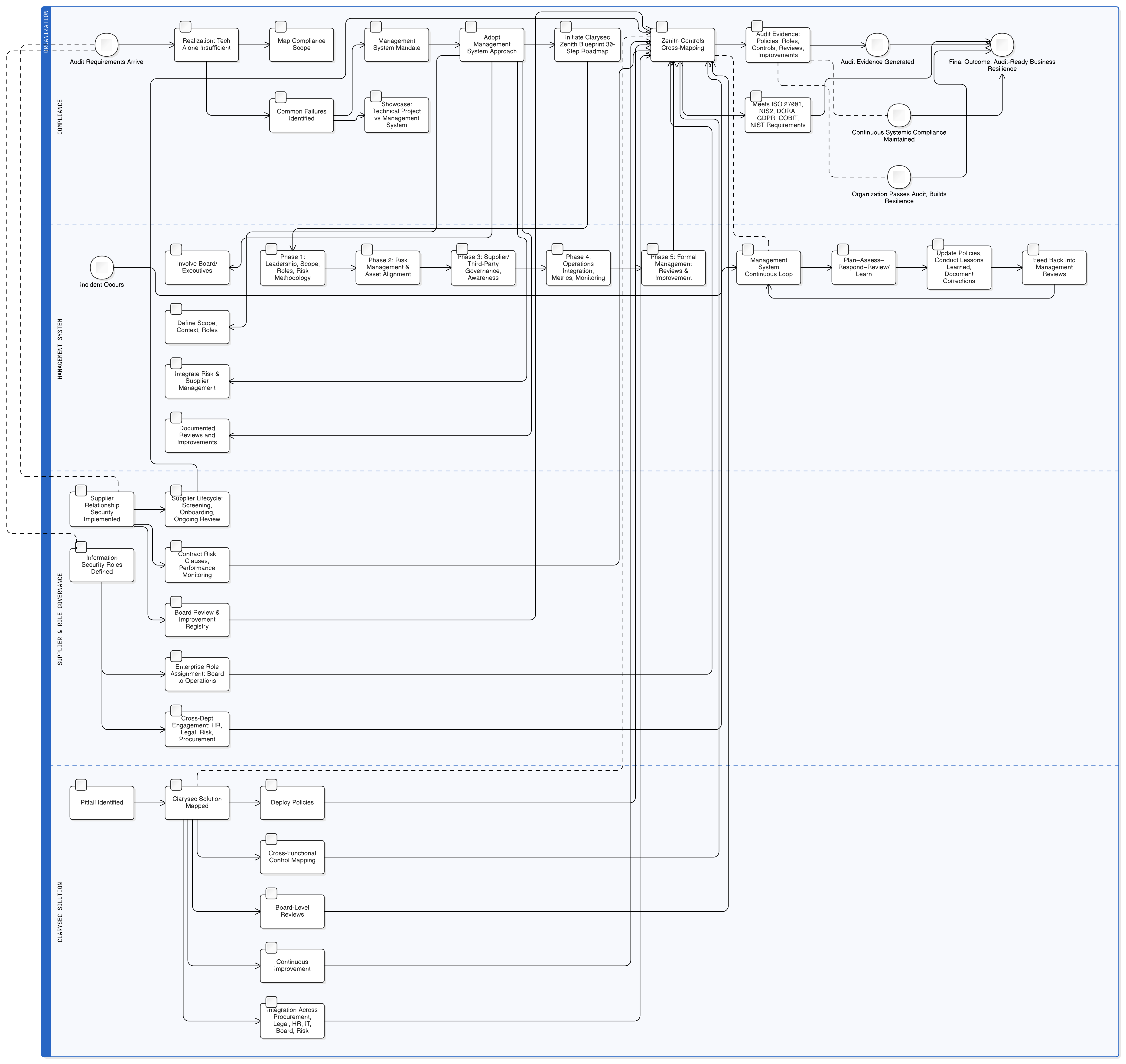
Audit disasters aren’t caused by weak firewalls, they’re the result of treating compliance as a tech checklist. Discover Clarysec’s management system strategies, mapped controls, and practical policies for seamless ISO 27001, NIS2, and DORA compliance.
When Simulation Meets Reality: The Crisis That Exposed Security Blind Spots
It was 2:00 PM on a Tuesday when Alex, the CISO at a fast-growing FinTech firm, was forced to stop their ransomware simulation. Sparks were flying on Slack, the board watched with growing alarm, and the DORA compliance deadline hovered menacingly. The simulation, intended to be routine, had snowballed into a showcase of vulnerabilities: entry points went undetected, critical assets weren’t prioritized, the communication plan failed, and supplier risk was murky at best.
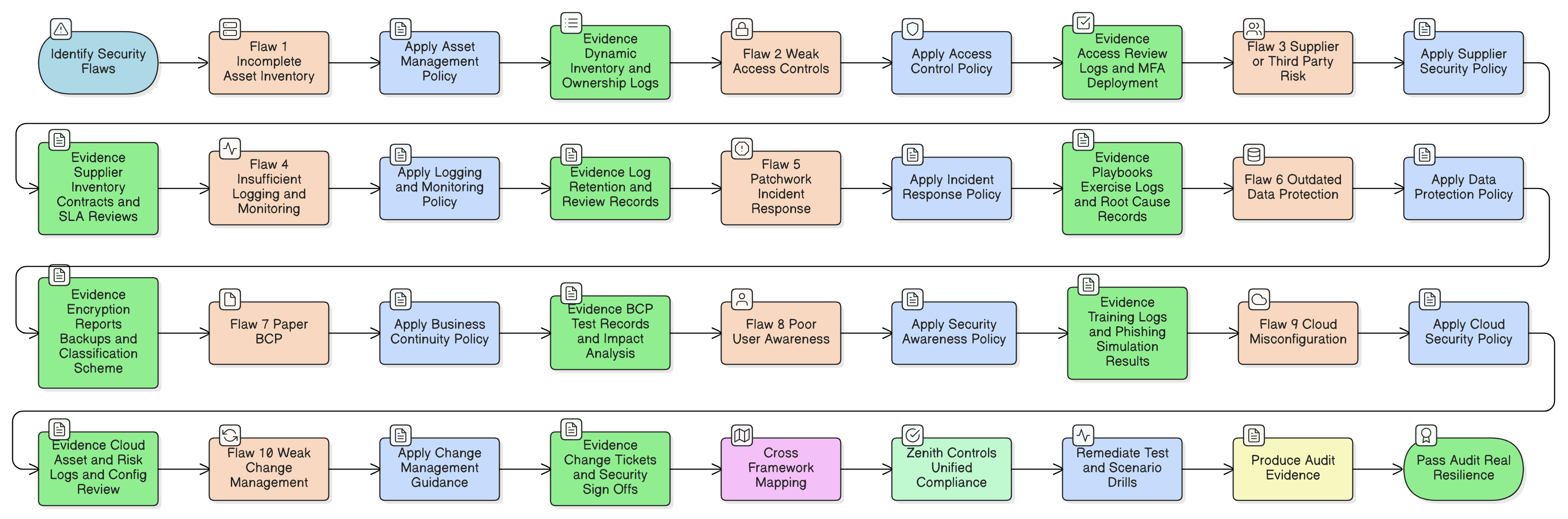
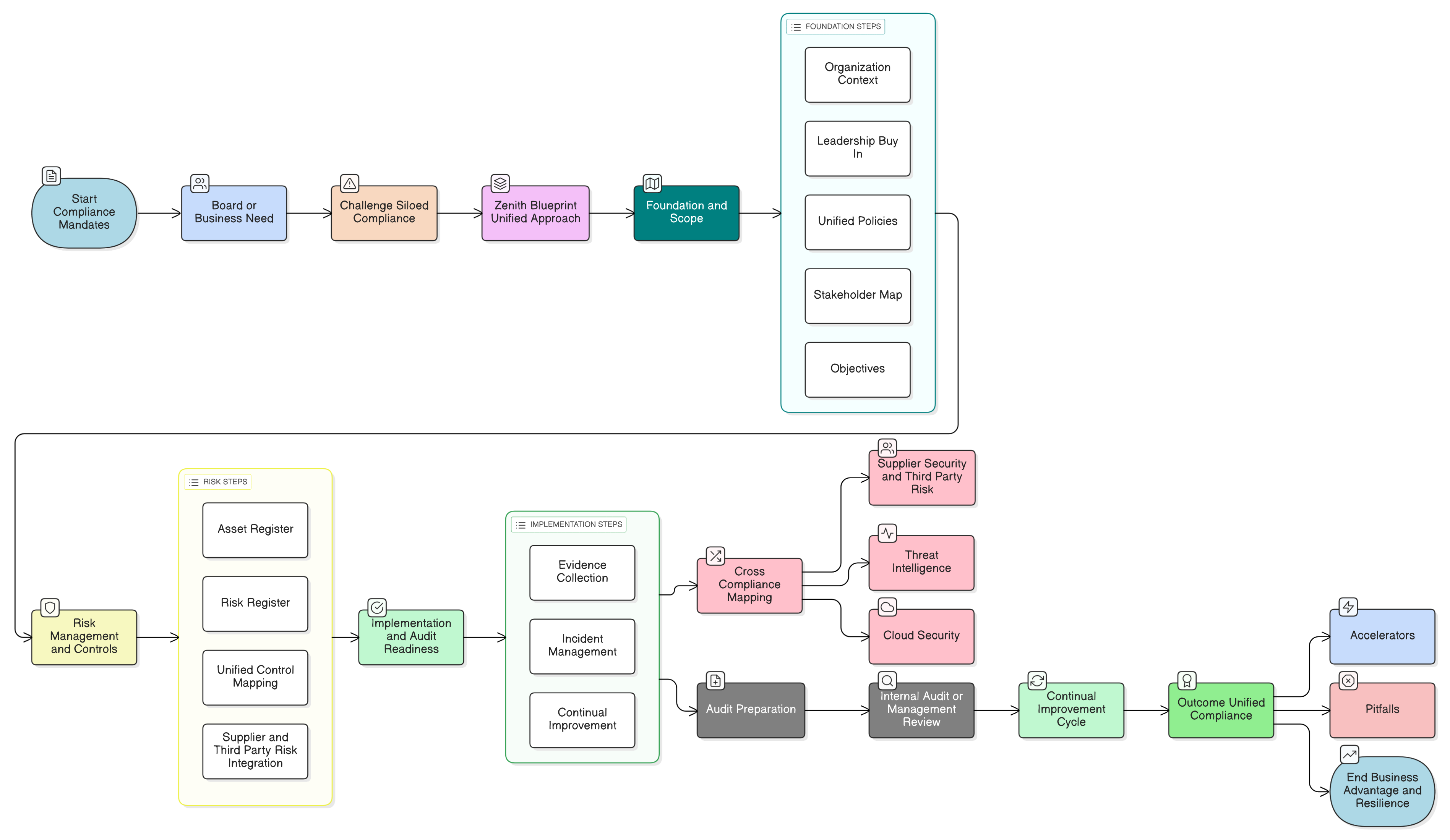
Clarysec’s Zenith Blueprint delivers the fastest and most reliable unified compliance for ISO 27001:2022, NIS2, and DORA. Discover actionable steps, control mappings, and real-world scenarios for CISOs and business leaders to achieve true audit and operational readiness.
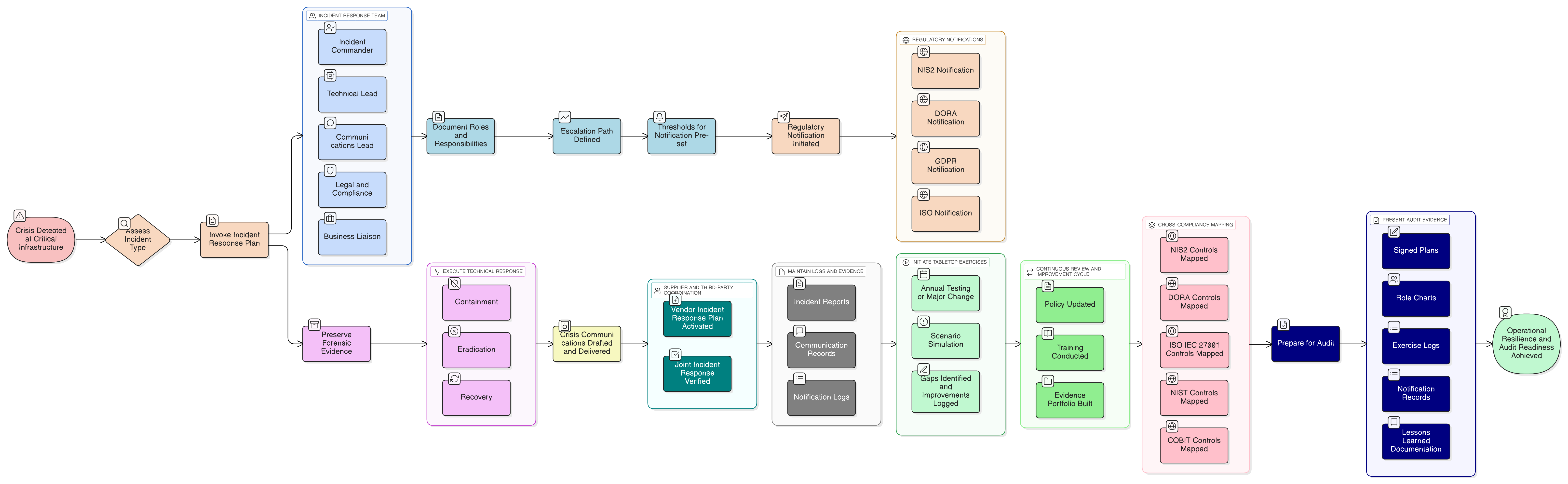
Unify your incident response strategy for NIS2, DORA, and ISO/IEC 27001:2022 compliance with Clarysec’s tested practices, actionable mappings, and robust policies. Includes real-world scenarios, practical checklists, and evidence-generation steps for audit readiness.
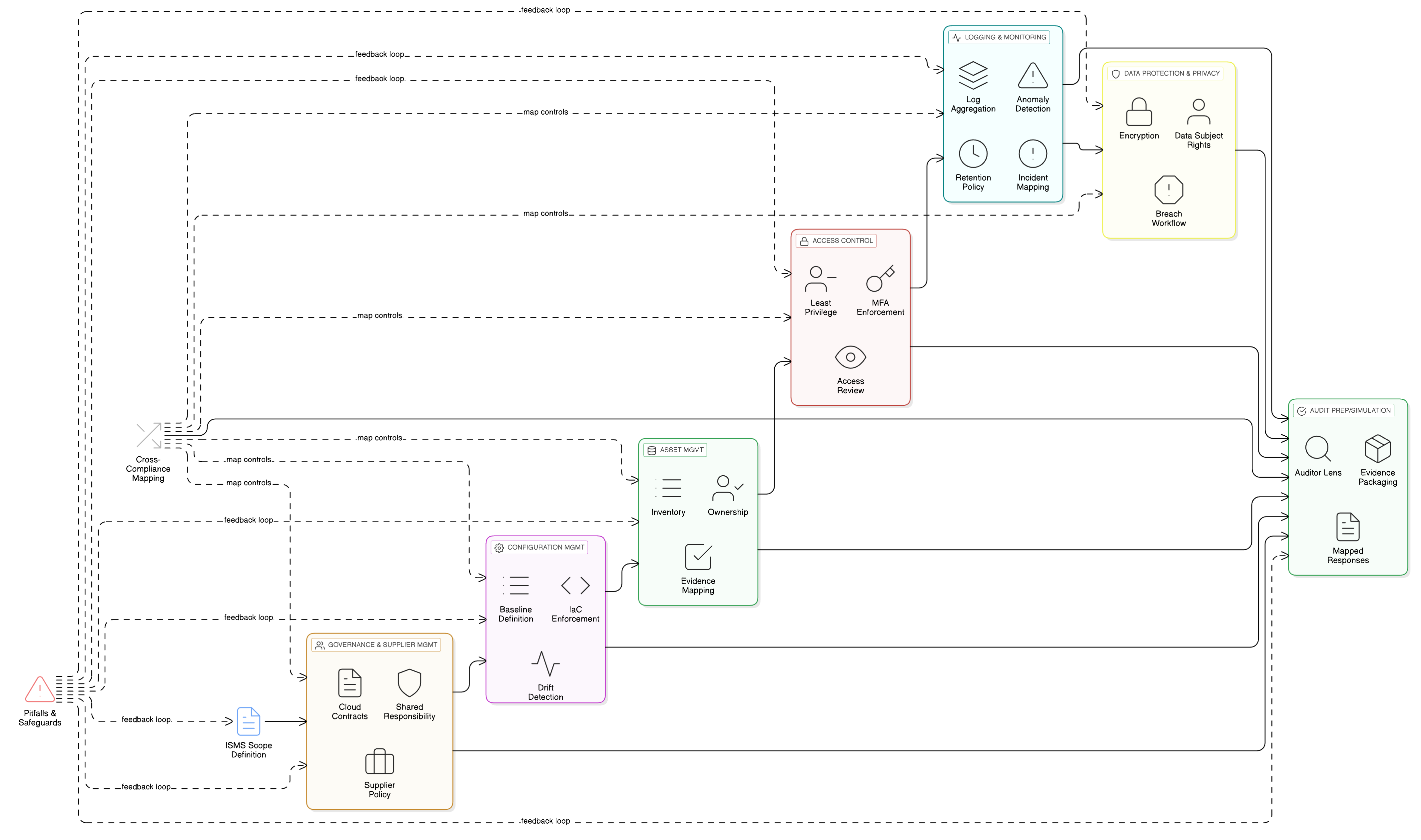
CISOs, compliance managers, and cloud architects: discover how to operationalize ISO 27001:2022 cloud controls for perpetual compliance. Real-world stories, technical mapping tables, and actionable blueprints from Clarysec unite security, governance, and audit-readiness across frameworks.